
In the last two weeks, we’ve seen what a SOC is and the difference between a Security Operations & Optimization Centre. All these discussions pointed to one key aspect: monitoring and early detection. But how do we monitor effectively? The answer lies in “logs.” Logs are crucial for monitoring and detecting user or device behaviour. Cybercrime is on the rise, putting businesses of all sizes and types at risk. To combat this threat, having a reliable security platform is essential.
So, what tools can forward these logs? There are many options available online, such as Splunk, Datadog, Sentinel One, Wazuh etc. Our focus today will be on the Wazuh tool today.
Wazuh is a dynamic security platform designed to protect businesses of all sizes from cyber threats. With its user-friendly interface and rich features, it offers customized solutions to meet various business needs. It is all-in-one open-source tool, which delivers extensive threat detection, visibility, and response capabilities.
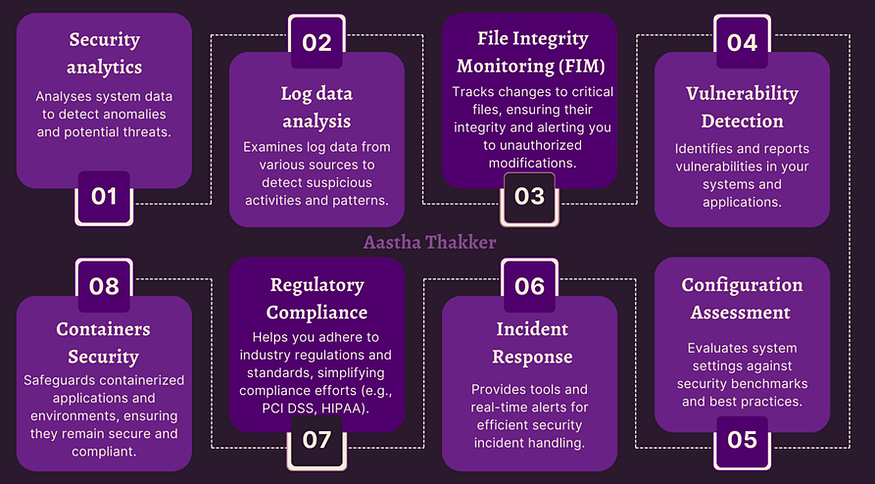
Capabilities of Wazuh
Types of Security Platform provided:
- All-In-One:
This platform integrates all security components into a single package. It includes the Wazuh manager, Elastic Stack, and the Wazuh agent. It does everything in one place. This means all the security features are on one computer. Ideal for small to medium-sized environments where managing multiple servers separately isn’t necessary. - Distributed:
Components are spread across different servers. The Wazuh manager, Elastic Stack, and agents operate on separate machines. Each part does a specific job. This is good for larger systems because it can handle more data and work faster. It’s like having a team where everyone has a role. - Centralized:
The Wazuh manager and Elastic Stack are centralized, while the agents are deployed across various endpoints. Best for environments with numerous endpoints, ensuring centralized control and monitoring while distributing agents. All the information from different parts of your system comes to one place. It’s useful for managing and seeing everything in one spot. - Cluster:
Involves multiple Wazuh managers working together in a cluster, providing redundancy and load balancing. This is similar to distributed but with a focus on high availability. It means Wazuh can keep working even if one part fails. It’s like having backup systems in place. Critical for large-scale enterprises requiring high availability and disaster recovery capabilities.
Wazuh Components
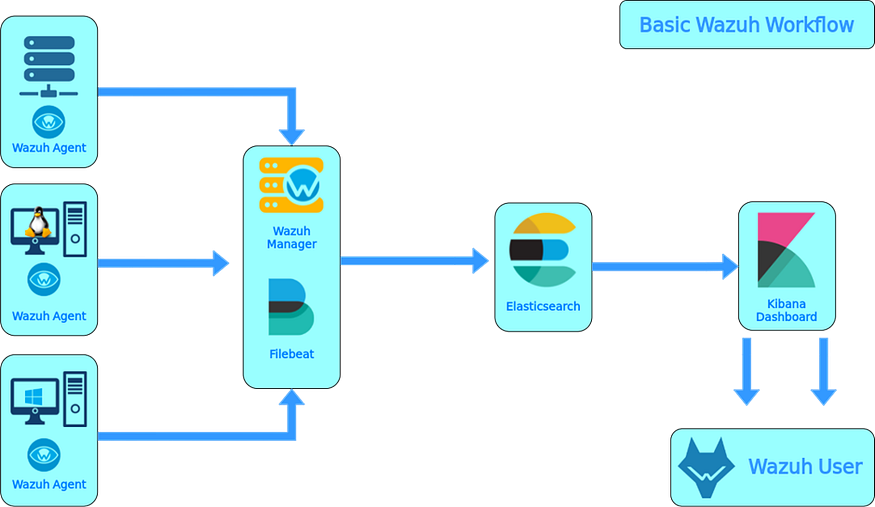
1. Data Collection and Monitoring
- Wazuh Agent:
The Wazuh Agent is installed on endpoint devices to gather security-related data from sources like system logs, network traffic, and system processes. It works on various devices, including servers, desktops, laptops, and mobile devices. The agent sends this data to the Wazuh Manager for analysis, either in real-time or at scheduled intervals. It is lightweight and has minimal impact on system performance, making it suitable for endpoint devices. - Filebeat:
Filebeat is a lightweight tool used to collect and forward log data to different destinations. In the Wazuh context, it collects log data from endpoints and sends it to the Wazuh server for analysis. The Wazuh server has pre-built Filebeat modules for common data sources like Apache web server logs, MySQL database logs, and system logs. These modules are easily configurable to start collecting data. Additionally, Wazuh provides a custom Filebeat module for collecting Windows event logs, which can then be forwarded to the Wazuh server for analysis.
2. Central Management and Analysis
- Wazuh Manager:
The Wazuh Manager is the central control point for the Wazuh platform. It handles the management of agents, rulesets, and notifications. It collects data from agents, analyzes it, and stores it in a database. The manager can send alerts to administrators via email, SMS, or other methods. It features a web-based interface for administrators to manage the platform, providing dashboards, reports, and system settings. The manager is highly scalable and can support thousands of agents, making it suitable for large organizations. - Wazuh Server:
The Wazuh Server analyzes data from the agents and triggers alerts when threats or anomalies are detected. It also remotely manages the agents’ configurations and monitors their status. The server uses threat intelligence to improve detection and enriches alert data with frameworks like MITRE ATT&CK and compliance requirements such as PCI DSS, GDPR, HIPAA, CIS, and NIST 800–53. This provides helpful context for security analytics. The server can integrate with external software like ServiceNow, Jira, PagerDuty, and Slack to streamline security operations. It consists of components for enrolling new agents, validating agent identities, and encrypting communications between agents and the server. - Analysis Engine:
The Analysis Engine is the server component responsible for analyzing data. It uses decoders to identify the type of information being processed, such as Windows events, SSH logs, and web server logs. These decoders extract relevant data elements from log messages, like source IP addresses, event IDs, and usernames. The engine then applies rules to identify patterns in the decoded events that could trigger alerts or call for automated countermeasures, such as banning an IP address, stopping a process, or removing malware. - Wazuh Ruleset:
The Wazuh Ruleset is a collection of rules designed to detect and alert on security events. It is customizable and can be tailored to meet the specific needs of an organization. The ruleset contains over 2000 rules covering a wide range of security events, including malware, suspicious behavior, and system vulnerabilities. It is regularly updated to stay effective against the latest threats. Organizations can also create custom rules to address their specific security requirements. The ruleset is crucial for detecting security threats within the Wazuh platform.
3. Data Storage and Indexing
- Wazuh Indexer:
The Wazuh Indexer is a powerful search and analytics engine designed to handle large amounts of data. It indexes and stores alerts from the Wazuh server, enabling quick data searches and analytics. The indexer can operate as a single-node or multi-node cluster, making it scalable and reliable. It stores data as JSON documents, with each document containing key-value pairs. These documents are organized into collections called indexes and are distributed across containers known as shards. By spreading documents across multiple shards and nodes, the Wazuh Indexer ensures redundancy and protects against hardware failures, while also improving query performance. - Archival Data Storage:
The Wazuh server stores both alerts and other events in files. These files can be in JSON (.json) or plain text (.log) format. The files are compressed and signed daily using MD5, SHA1, and SHA256 checksums to ensure data integrity. This method provides an additional layer of data storage and security beyond what is sent to the Wazuh Indexer.
4. User Interface and Visualization
- Wazuh App:
The Wazuh App is a user-friendly interface that lets you access data collected by Wazuh. With this web-based app, you can view alerts, manage agents, and customize rulesets. It offers dashboards displaying key security metrics like the number of alerts, agents, and the severity of alerts. The app also provides customizable reports to meet specific needs. It is highly customizable, allowing organizations to tailor it to their specific requirements. - Wazuh Dashboard:
The Wazuh Dashboard is a web interface for analyzing and visualizing security events and alerts. It helps in managing and monitoring the Wazuh platform. The dashboard supports role-based access control (RBAC) and single sign-on (SSO). It includes pre-configured dashboards for regulatory compliance (such as PCI DSS, GDPR, HIPAA, and NIST 800–53) and provides an interface to navigate the MITRE ATT&CK framework and related alerts.
5. Integration and Extension
- Wazuh API:
The Wazuh API is a RESTful interface for accessing data stored in the Wazuh database. It allows developers to create custom applications using the data collected by Wazuh. Through the API, you can retrieve information about agents, alerts, and events, as well as manage rulesets and notifications. The API is well-documented and supports multiple programming languages, including Python, Ruby, and Java, making it easy for developers to integrate Wazuh into existing security systems.
6. Scalability and High Availability
- Wazuh Cluster Daemon:
The Wazuh Cluster Daemon enables horizontal scaling of Wazuh servers by deploying them as a cluster. This setup, combined with a network load balancer, provides high availability and load balancing. The cluster daemon allows Wazuh servers to communicate and stay synchronized, ensuring seamless operation and reliability.
7. Security and Access Control
- Agent Enrollment Service:
The Agent Enrollment Service is responsible for enrolling new agents in the Wazuh system. It assigns and distributes unique authentication keys to each agent. This service operates as a network service and supports authentication through TLS/SSL certificates or a fixed password. - Agent Connection Service:
The Agent Connection Service handles data received from agents. It uses the keys provided by the enrollment service to verify each agent’s identity and secure communications between the Wazuh agent and server. Additionally, it allows centralized management of agent configurations, enabling remote updates of agent settings.
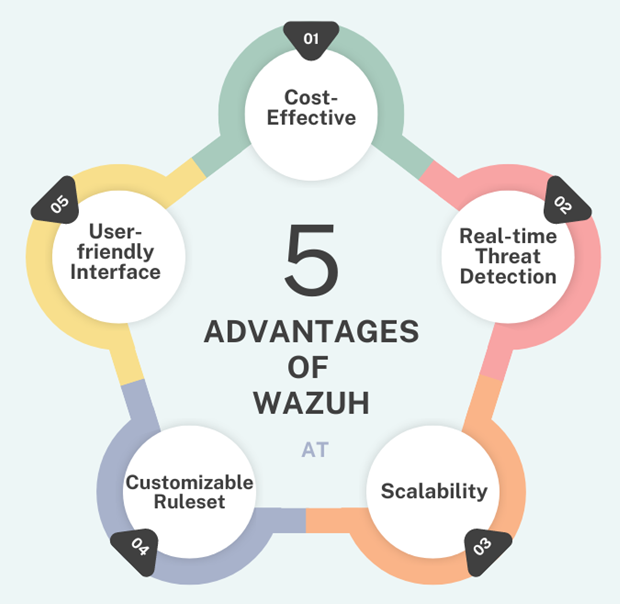
Advantages of Wazuh
Next week, we will learn how to create rules and trigger logs. For this, you will need Ubuntu (as a Wazuh agent) and RHEL v8 or 9 (as a Wazuh server). If you have these prerequisites, you can follow along with the next steps.