Introduction
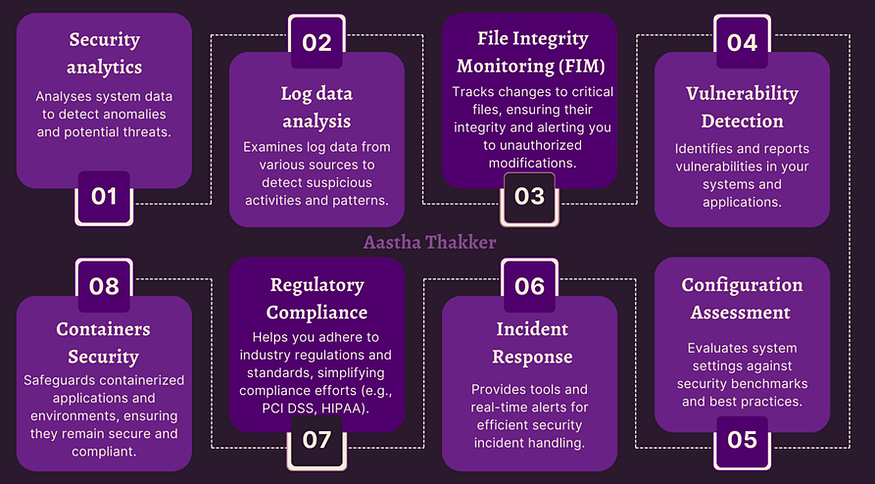
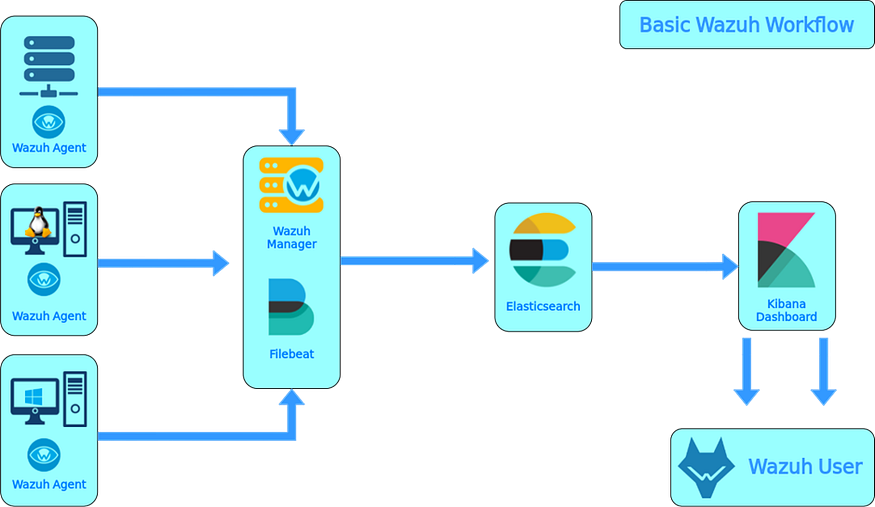
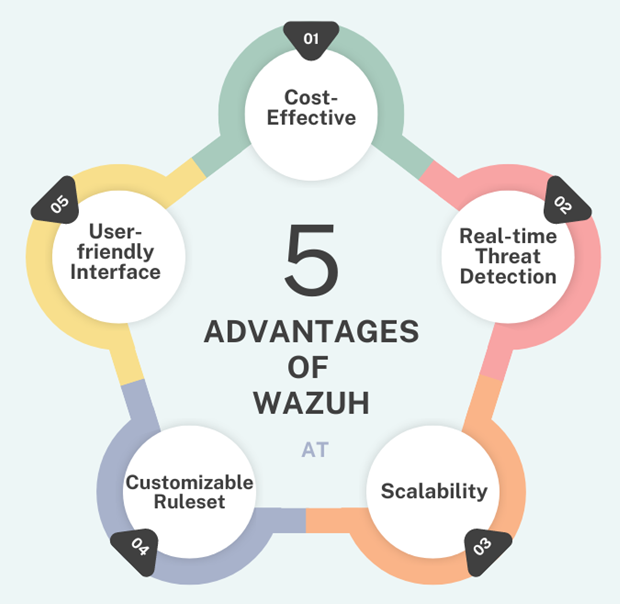
In modern cybersecurity, centralized log management is crucial for monitoring network activities and detecting potential threats. Wazuh, an open-source security platform, provides powerful log analysis and threat detection capabilities. By integrating pfSense, a widely used open-source firewall, with Wazuh via Syslog, administrators can enhance network visibility and security monitoring.
This guide will walk you through the process of configuring pfSense to send logs to Wazuh.
Configuring pfSense to Send Logs to Wazuh via Syslog
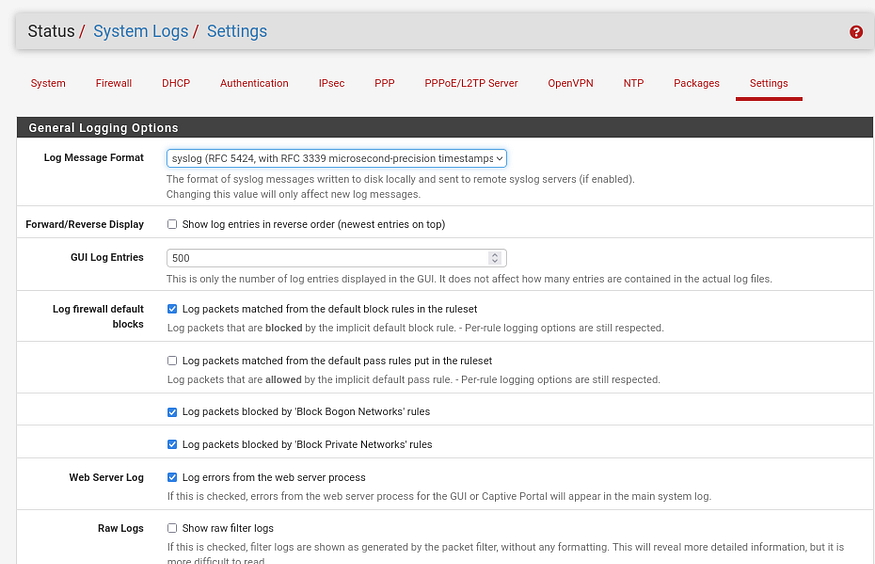
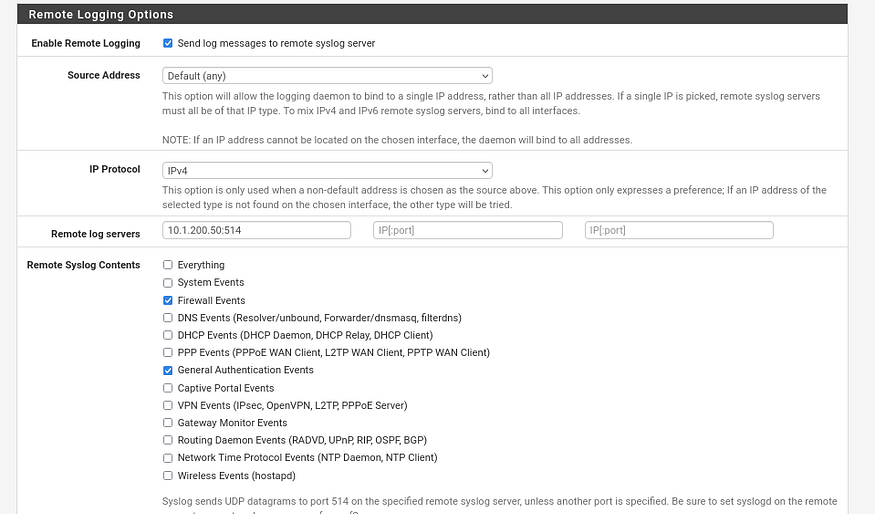
To enable remote logging in pfSense, navigate to Status → System Logs → Settings and scroll down to the Remote Logging Options section. Check Enable Remote Logging, then enter the IP address of your Wazuh server (e.g., 10.1.200.50) in the Remote Syslog Servers field. Set the Remote Syslog Port to 514, which is the default for Syslog. Next, select the log facilities you want to send, such as Firewall, System, and DHCP. For better compatibility with Wazuh,Don’t forget tp choose the RFC 5424 format. Finally, save the settings to apply the configuration.
Configuring Wazuh Server to Receive pfSense Logs

To configure Wazuh to receive logs from pfSense, edit the ossec.conf file on the Wazuh server. In the <remote> section, add the Syslog connection with port 514, using the UDP protocol, and set the allowed IP to the pfSense interface IP (e.g., 10.1.200.254). The local IP address of the Wazuh server should match the one set in the pfSense remote logging settings. After saving the changes, restart the Wazuh Manager and check the logs to confirm that pfSense logs are being received. If you see the logs, the setup is successful.
Testing Log Reception on Wazuh Manager with tcpdump
To verify that pfSense logs are reaching the Wazuh server, use tcpdump to capture Syslog traffic. Run tcpdump on the Wazuh server to listen for UDP packets on port 514, ensuring logs are being transmitted. If packets from the pfSense IP appear in the output, the connection is successful. Otherwise, check pfSense’s remote logging settings and firewall rules.

Creating a Decoder and Rules for Matching pfSense Logs in Wazuh
We created a decoder and rules in Wazuh to properly analyze and categorize pfSense logs. By default, Wazuh may not recognize pfSense logs correctly, as they have a specific format. The decoder helps extract important details like source IP, destination IP, and protocol from the raw logs. The rule then matches specific events, such as blocked traffic, and assigns them a severity level. This allows Wazuh to generate alerts for security-relevant events, making it easier to monitor and respond to potential threats in the network.




pfSense Logs Successfully Integrated with Wazuh

Note: While it is possible to install the Wazuh agent directly on pfSense, it is not recommended due to compatibility and performance concerns. pfSense is a firewall appliance, and adding extra software like the Wazuh agent may affect its stability and security. Instead, using remote Syslog logging to send logs to a dedicated Wazuh server is the best practice for efficient monitoring without impacting pfSense’s performance.